9 June, 2004: A question of presentation
In the comments to an earlier piece, Dave Weeden raises an important question:
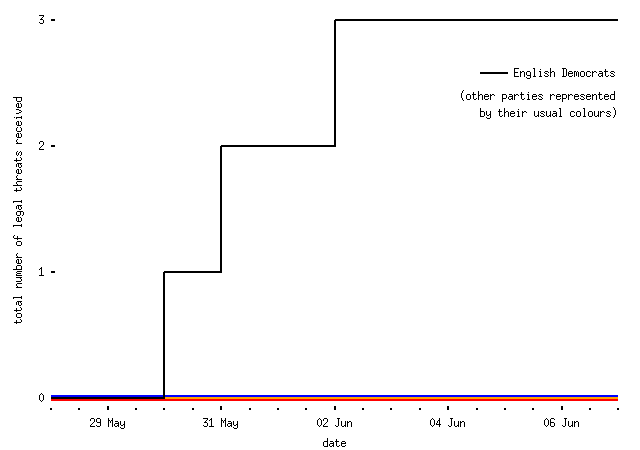
Surely after all this correspondence with the English Democrats, it's now possible to draw a graph of some kind?
Legal threats received, by date and sending political party
9 June, 2004: Miscellany, yet again
Some random, undirected thoughts:
-
A question I put at NotCon to Cory Doctorow, who believes the thesis that technologies have politics: in particular that inventions like the printing press and the internet are fundamentally technologies of the liberal enlightenment, and that technologies like `trusted computing' are fundamentally repressive. Anyway:
Technologies may or may not have inbuilt politics. The printing press can be used for printing books, or printing identity cards; `trusted computing' can be used to enforce digital rights management or to secure peer-to-peer networks. If these technologies do have political values, how can we tell ahead of time what they are?
-
I also spoke to a couple of people there who were working on (or enthusiasts for) heavily-encrypted, impossible-to-snoop peer-to-peer (`filesharing') applications. A well-known example is FreeNet; there are various others. FreeNet describes itself as,
free software which lets you publish and obtain information on the Internet without fear of censorship. To achieve this freedom, the network is entirely decentralized and publishers and consumers of information are anonymous. Without anonymity there can never be true freedom of speech, and without decentralization the network will be vulnerable to attack.
-- which is a point of view, I suppose. A lot of people who work on this sort of thing have the ambition of making it impossible for record companies to threaten them when they send copies of music to their friends; while, as ever, I must point out that copyright infringement is Bad and Wrong and nobody ought to do it, the idea of giving the RIAA a black eye over their (frankly brutish) tactics is a worthy one.
But I think these people are addressing the wrong problem. If you build a secure, anonymous peer-to-peer network that actually works and is convenient to use, the result will be quiet panic among the Powers That Be, swiftly followed by oppressive regulation. While the advocates of this kind of technology will talk about how useful they are for enabling political free speech, the content industries will claim that they enable piracy and the police will warn about their usefulness to criminals. Peer-to-peer advocates will not win this argument; they will face arguments not about Chinese dissidents speaking freely through the network, but about child pornographers and terrorists distributing photographs of children being raped and bomb-making instructions. Government will run, not walk, to implement yet another technically dumb but crowd-pleasing bit of legislation to allow them to shut the thing down or bug every computer connected to it; and every day they delay doing so, the tabloid newspapers will scream for their blood. And you know what? They might be right, at least in part.
People who want to really irk the record industries -- and I'll remind you that copying music in infringement of copyright is Bad and Wrong and you mustn't do it -- should work not on theoretically sound but politically dangerous systems, but on subverting protocols which are so useful that they won't be regulated away. For instance, in a record-industry fantasy world, laws could force ISPs to prevent their customers from running any servers at all (by dropping incoming packets with the SYN flag set, if you want to know), unless they were licensed by some body which ensured that they weren't doing anything wrong. (I don't think this is likely, even in the United States, but it is possible; if it did happen, it would be justified by the same arguments about enforcement of the criminal law that I describe above.) This would kill all the current peer-to-peer systems, but leave most of the Internet's `killer applications' workable (though much more expensive to run).
But imagine instead building such a network built on email. People expect to be able to email (for instance) large `Power Point' presentations to one another, and what's to say whether a sound embedded in such a file is an infringing copy of a song, or a legitimate sound-effect? While we shouldn't expect email to carry on working in exactly the same way as it has for the last thirty years (though the infrastructure has proved remarkably resilient) I think it's reasonable to expect that there will still be something like email, with more-or-less the same functionality and user interface, for at least that long. And people will rely on it (as they rely on email now) and be very intolerant of interference with it. I had more technical thoughts about this a while ago, which may be of interest to the technically-minded.
- In the unlikely event that you haven't seen it, go and play with They Work For You, Hansard done properly. All praise to Francis and all the other volunteers for a fantastic piece of work, and to mySociety for getting the project going.
-
And now I've bored my half-dozen readers to tears with all that technical stuff (and, coincidentally, it was nice to meet some of you face-to-face on Sunday), a political thought. I've just received a piece of election literature from the BNP. On the back of this odious document is a profile of the Unterkartoffelfuhrer who's standing for election here, complete with a picture of his smiling family including two small children. One of the kids is quoted as saying,
My Dad isn't a racist!
Presumably the kid then continued,
He just doesn't like black people or foreigners.
but the BNP didn't see fit to quote this. So there we are: the BNP, a party so hopeless that their election literature is written by six-year-olds.
- And something slightly more trivial. I note that the UK Independence Party are now routinely referred to as `you-kip' in the media. Is this something they endorse, or is it a bit of linguistic viral marketing designed to make them sound silly, like those people who refer to flying saucers as `you-foes'?